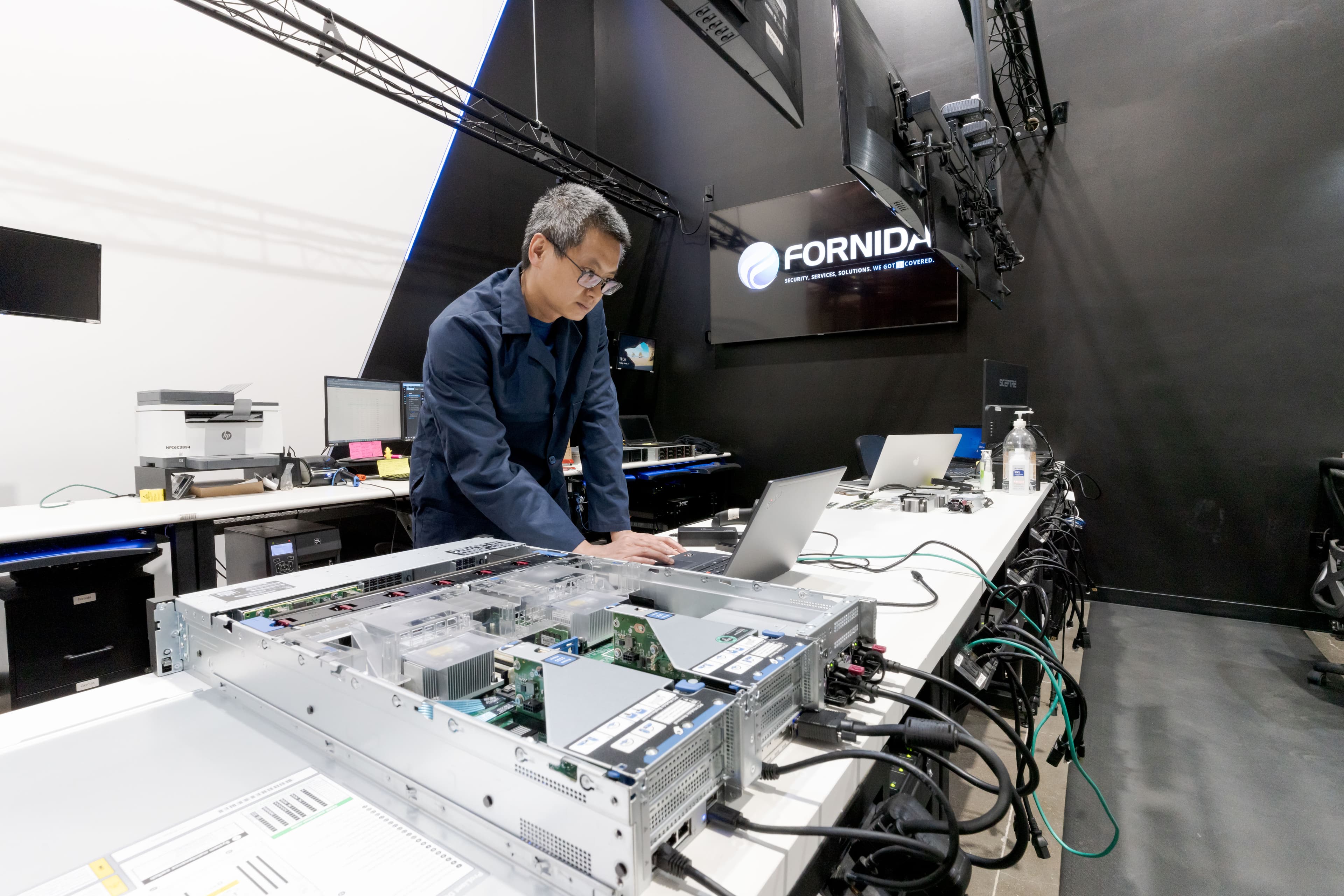
Layered cybersecurity for real business operations.
Fornida protects SMBs across endpoints, email, identity, networks, monitoring, backups, incident response, and recovery planning — with security built into the way your business actually works.
The attack surface now includes everyday tools, accounts, and workflows.
What Fornida protects
Endpoint detection
Email & identity security
SOC monitoring
Backup & recovery
Incident response & restoration
AI governance & security
Security is not a product. It is an operating discipline.
Review endpoints, identity, email, network, backups, tools, and current risk posture.
Implement layered controls across users, devices, accounts, email, and infrastructure.
Use monitoring, alerts, and vendor tools to identify suspicious behavior in real time.
Escalate, contain threats, and help restore operations when incidents happen.
Secure AI adoption starts with a secure operating environment.
If employees are using AI tools on unmanaged devices, with scattered files and weak identity controls, AI can increase risk.
Fornida helps businesses strengthen the foundation before automation expands the number of systems, workflows, and data pathways in motion.